Facility access and building security is an important component for any office, warehouse, retail space, medical clinic and more. Ensuring the safety of not only employees and guests, but also the content within the building is critical to the success of the business. Building a facility access system may seem like a daunting task, especially to small businesses who do not always have the resources to properly manage these systems. Grandstream is here to help. Our facility access and security solutions are easy to setup and provide centralized management options that can be configured for small to large deployments.
With the global COVID-19 pandemic and a shift in the increase in remote workers, businesses need to find a way to ensure that WFH security practices are put in place. Not only do individual workers need to be more aware of online attacks, but IT teams need to adjust and make certain that their business infrastructure, data and communications are secure. Check out the tips below for how your business can build a secure WFH solution for remote workers.
Topics: Security, remote work
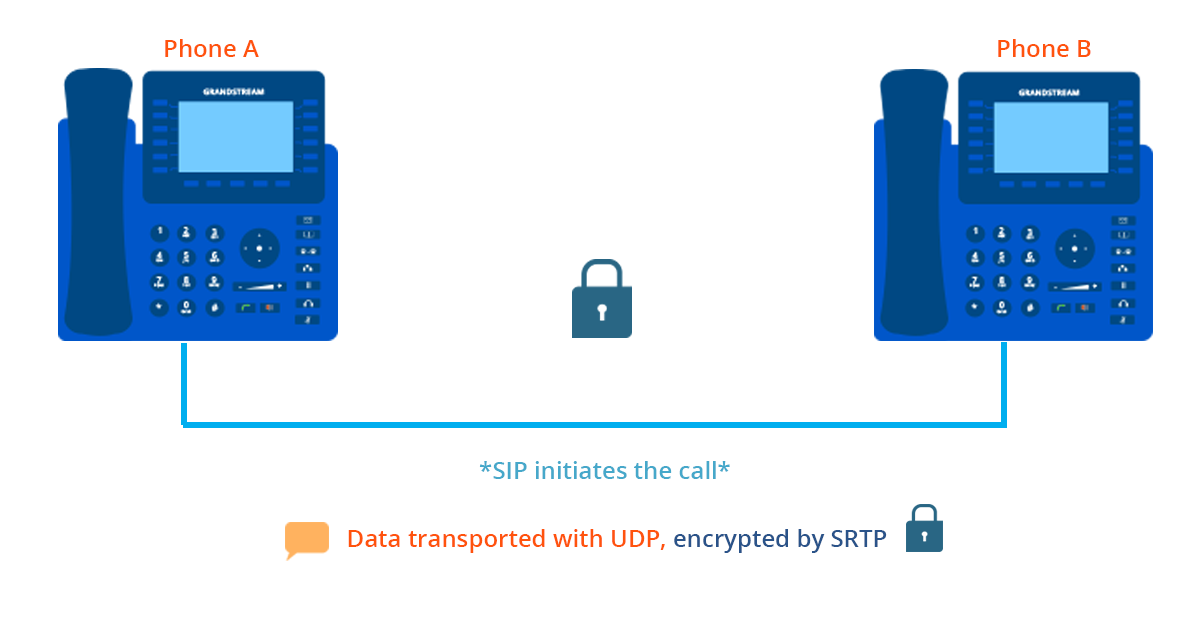
Let’s face it, security in VoIP is a top concern, especially when multiple locations and users are connected under the same network— if something goes wrong, that means your entire system and everyone in it is affected. Thankfully, with the right security practices, keeping your VoIP network safe and protected doesn’t have to be messy. Today, I am going to list the most effective ways to keep your VoIP network secured and how you can apply these best practices to your own communication hub.
Topics: VoIP, Security, Best Practices, tips, voip network
When discussing a UC solution with a customer, security is likely a top concern of theirs. In recent years, it seems as if the more information we put over the Internet, the more vulnerable we become. However, trying to explain cryptographic protocols to someone without a VoIP background can get a bit dicey, and it’s easy to get lost in a sea of acronyms. For today’s blog, let’s discuss a brief overview of VoIP communication and encryption at an accessible level.
Topics: Security, Unified Communications, IP Voice, IP communications
The success of technology is based on constant advancement. Right now, the industry is looking toward the future in anticipation of what the “newfound” cloud will bring. IP Telephony is no different as more and more communications move to the cloud. This leads many to question, is hardware going to stick around? The on premise IP-PBX isn’t going the way of the tin can, and Grandstream proves that—the arrival of the cloud doesn’t cancel out the benefits of hardware-based solutions. But I suppose for some, the question remains how does the on premise IP PBX innovate with us? The answer to that is through customization, security, and flexibility.
Topics: Security, Unified Communications
We’ve already started the conversation about security— now, let’s focus on loss prevention for businesses. Part of a good risk management strategy is to reduce threats from both outside and inside the organization. This is where video surveillance comes in.
Topics: Security, IP Surveillance
Like any technology, WiFI has its own share of security concerns. The nature of wireless networks allows hackers or anyone with malicious intent to locate themselves close to an access point in order to infiltrate a network. According to Kasperksy, approximately 24.7% of Wi-Fi hotspots in the world do not use any encryption at all, and that does not even include the WiFi networks that are under-secured. More than 80 percent of U.S. companies have been successfully hacked, according to a Duke University/CFO Magazine Global Business Outlook Survey. Additionally, a survey by PricewaterhouseCoopers in early 2017 found that there has been a 38% increase in the instances of phishing scams and other cyber security incidents from 2015 to 2016.
In my previous WebRTC post I provided an overview from a simplified, easy-to-understand perspective. But today, I thought it would be pertinent to discuss the hefty security features of WebRTC. It’s safe to say, that with data breaches, ransonware, and phishing schemes dominating the news security and protection is at front of mind. Being that WebRTC is an open-source API it’s important to highlight features that make it an attractive, but secure option.
Topics: Security, Cloud Services
Integration has become a popular buzzword within a lot of industries, especially technology. Webster’s dictionary defines the term “integrate” as “to combine one thing with another so that they become a whole,” but I think there is a better definition when it comes to technology. Integration is “to combine one thing with another so that they each become better.” The real benefit of technology integration is giving each piece the ability to do something it could not do before thanks to its ability to work with other products, services, apps, and more. Within the SIP and UC world, we are well-versed in integration. However, while we are often looking for ways to integrate our SIP communication products together, the market has overlooked the fact that SIP communication can be leveraged to offer powerful security and facility access tools. One simple product, a SIP Video Door Station like our GDS3710, allows you to easily accomplish this.
Topics: Security, IP Surveillance, Facility Access
You might have seen the term VPN thrown around lately. A quick Internet search explains that VPN is a Virtual Private Network that allows the exchange of encrypted data through a VPN server. A pretty cool concept considering the browsing security issues that have been flooding our media. All this talk about data consumer protection laws, the aftermath of whistleblowers and the overall security concern in our online culture has sparked discussions about VPN.























.webp?width=250&height=131&name=how-to-use-gdms-q1-2024%20(1).webp)